No one may be subjected to arbitrary interference with his private life, his family, his dwelling and his correspondence or impairments to his honor and reputation. Everyone is entitled to legal protection against such interference or interference.
This is Article 12 of the Universal Declaration of Human Rights in UN Resolution 217 A (III) of 10 December 1948, which was also approved by the 1950 European Convention for the Protection of Human Rights and Fundamental Freedoms (ECHR).
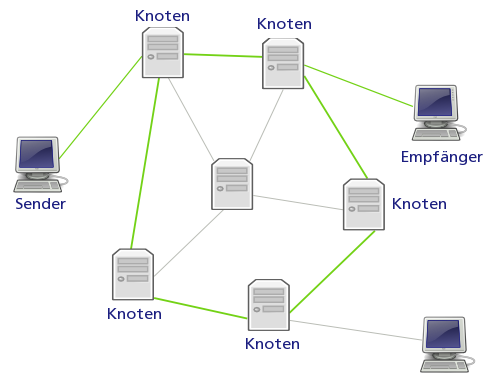
But the very circumvention of this principle is made very easy when sending mail. The reading and tracking of e-mails is in principle possible at each node (mail server, proxy, router), and this happens not infrequently: Since January 1, 2005, for example, all e-mail providers with more than 1000 customers are required to provide technical solutions that grant access to all customer e-mail traffic to state institutions.
In addition to the state-organized actions, there are a number of other snoopers. Economic interests often play a major role here. For example, paid crackers, analytics companies or even bored administrators are snooping in your network lanes. And, even that is a difference to the classic post: the email is - in contrast to an open letter - not recognizable that it was intercepted and read.
Finally, with traditional mail, important documents are not sent as a postcard, but in an envelope and at best with a personal transfer note. So one wants to achieve that the documents actually only reach those for whom they are intended, and the receiver can also check whether the transmitter is genuine.
To show that this and much more is also possible with mails and files and how this is technically implemented, these instructions should serve.